

TABLE OF CONTENTS
Sybil attack and Sybil resistance
-
Sybil attack and Sybil resistance
-
Typical approaches to counter Sybil attacks
-
Sybil resistance through proof of human-ness
-
A. Sybil attacks in airdrops
-
B. Sybil attacks in governance
-
C. Sybil attacks in Play-to-Earn (P2E)
-
Sybil-resistant IDs and their use cases
-
[Reference] The voting system of Optimism/Gitcoin
Primitives of Proof of Personhood
-
Positioning of PoP
-
Worldcoin
-
BrightID
-
Proof of Humanity
-
Comparison of each product
SSO (Single Sign-On) applications that aggregate user information
-
SSO and ID
-
Gitcoin Passport
-
Quadrata Passport
-
[Supplement] Information disclosure through DID (Decentralized Identity) and ZKP (Zero-Knowledge Proof
-
Author's Considerations
About this report
In this report, we focus on the theme of "Sybil resistance" and discuss how this concept should be applied in the current landscape of decentralized applications, based on existing challenges.
A Sybil attack is one type of attack that occurs in decentralized networks with anonymous participants. It refers to the creation of a large number of false identities (Sybils) in a decentralized system, which then influence decisions and votes within the system or network, distorting the intended decision-making and allocation of resources. Especially in the context of blockchain, each Sybil is recognized as an independent entity (address) by the system, allowing the attacker to wield significant influence through numerous Sybils.
In decentralized networks, cases related to the distribution of profits and rewards, such as mining, staking, airdrops, DAO voting, and crypto games, are prone to Sybil attacks. This arises from the characteristic that anyone can anonymously and freely participate in the network. At the base layer, systems like PoW (Proof of Work) or PoS (Proof of Stake) set appropriate entry requirements to address this challenge.
However, in decentralized applications, there is often a lack of robust Sybil resistance mechanisms as found in the base layer, leading to frequent Sybil attacks. In P2E (Play-to-Earn) games, cases where a single user utilizes multiple devices to generate substantial profits or, as seen in recent airdrops, a single user employs hundreds of addresses, have become strategies for maximizing profits.
Proof of Personhood (PoP) is an approach gaining attention as a method to prove that the owner of an address is an actual person. This category includes various methods such as biometric authentication, verification of government-issued ID credentials, and the establishment of trust-based networks.
By reading this report, you will be able to understand IDs with Sybil resistance, including PoP. In our previous CTAnalysis Web3 Social Research Report, we broadly explained mainly decentralized social, so please also take a look at that for a comprehensive understanding.
Sybil attack and Sybil resistance
What is SYBIL Attack?
The general understanding of Sybil attacks:
A Sybil attack is a form of attack that occurs in decentralized networks with anonymous participants. This attack involves creating a large number of fake identities (Sybils) within a decentralized system and using them to influence decisions and votes within the network, thereby distorting the legitimate decision-making process and resource allocation.
In blockchain, which is also a decentralized and anonymous network, each Sybil is recognized as an independent entity (address) by the system. This allows an attacker to use numerous Sybils to expand their influence.
In the Web2 world, user identification (ID) is centrally managed by corporations, allowing for top-down Sybil countermeasures. However, in crypto, with characteristics like "permissionless" and "anonymity," it is challenging to completely prevent the occurrence of Sybils, and solutions to this problem have been sought for many years.
Vectors for Sybil countermeasures in crypto:
Countermeasures against attacks in systems based on Web3 and other decentralized networks can be broadly divided into two directions. One is the design of systems that incorporate Sybil resistance. For instance, Bitcoin and Ethereum use PoW (Proof of Work) or PoS (Proof of Stake) to set a cost barrier for participating in network decision-making (such as block creation), thereby raising the hurdle for Sybil attacks.
While the base layer adopts PoW or PoS, there are no such entry costs in the application layer or DAO governance. Therefore, different approaches are being considered to achieve Sybil resistance by proving that the participant's address is based on actual human identity.
In voting systems where all users can freely vote, Sybils can easily participate, increasing the likelihood of distorting the decision-making process. To counter this issue, approaches such as biometric authentication and selective disclosure of information using ZKP (Zero-Knowledge Proof) are being considered to prove the human-ness of the user behind an address.
Typical approaches to counter Sybil attacks
To prevent Sybil attacks, strategies such as government-issued IDs, biometric authentication, ID based on social graphs, and resource-based approaches exemplified by Bitcoin mining are well-known. These solutions possess varying degrees of characteristics in terms of privacy and trust.
-
Government-issued ID

This refers to a system where countries or governments issue unique IDs to each individual, such as passports or ID cards. The advantage is that the reliability of the ID is established under the credibility of the national level. A disadvantage is that since a single organization manages it, there are concerns about privacy issues and the possibility of unfairness in the issuance of IDs to certain individuals.
-
Biometric (Biometrics) ID

This method proves the uniqueness of an ID through the authentication of individual users' biometric characteristics (face, fingerprint, iris, voiceprint). Biometric features are unique to each individual and are difficult to forge. However, these are highly sensitive pieces of information, so it is necessary to understand the risks related to privacy and false detections in systems managing biometric data.
Typical approaches to counter Sybil attacks
C. Trust-based IDs (such as those from social networks)
This is a system that evaluates the trustworthiness of a user by analyzing their social graph (such as relationships with friends and followers). It's challenging for Sybils to imitate a real user's social graph, providing a certain level of defense against them. However, since the social graph itself can contain sensitive information, the handling of privacy by the system becomes a concern.
D. Resource-based system
This system proves the existence of users through systems that require time and resources (such as computational power, storage, capital requirements). Bitcoin mining is an example of this approach, which increases the cost for attackers while not requiring any personal information from users. However, a significant drawback is that the cost of entry can be very high, creating economic barriers to access.
Sybil resistance through proof of human-ness
Proof of Personhood(PoP)
"Proof of Personhood (PoP)" is a concept used to prevent Sybil attacks in P2P networks. It provides a means to prevent the creation of fake identities and to prove that participants are unique humans. The concept was first introduced in 2014 by Vitalik Buterin, and it was formally published as a concept in 2017.
Users can acquire proof of this qualification by providing information to the issuing entity to prove that they are unique humans. By submitting this proof to verifiers, verifiers can verify the authenticity of a user's claim without requiring personal information about the user.
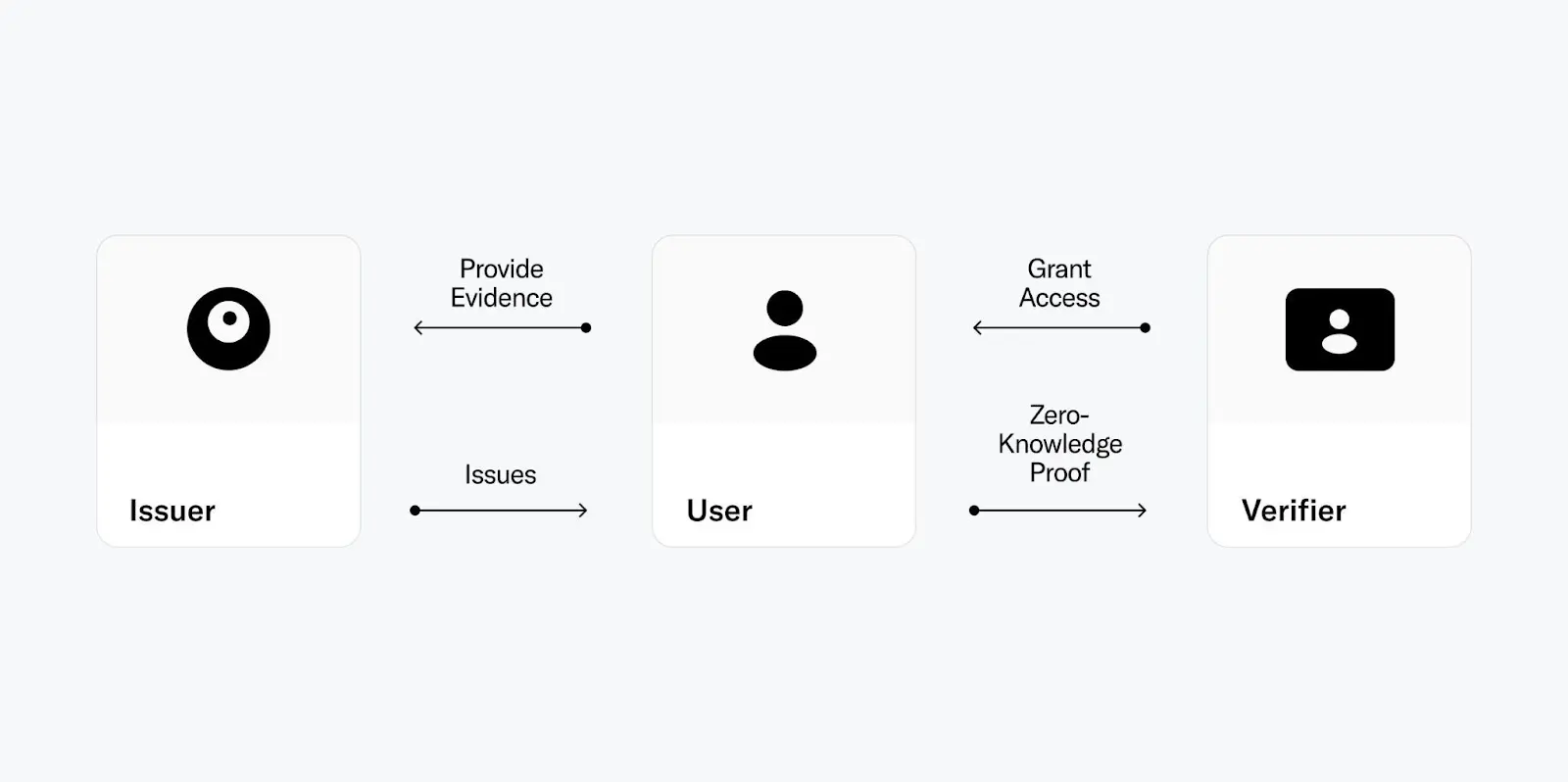
Image Image Source:Worldcoin
PoP can be expressed through various forms of proof, including biometric authentication, but it needs to ensure that it is accessible to everyone, that fake proofs cannot be created, and that only one proof can be created per user.
The introduction of PoP into products could potentially serve as the foundation for more equitable applications such as a democratic voting system where each person has one vote, a Universal Basic Income (UBI) system with one account per person, or a highly reliable social media platform.
A. Sybil attacks in airdrops
Acquisition of Airdrops Using Multiple Addresses
After the airdrop conducted by Uniswap in 2020, which was based on the user's product usage history, users began to learn the tendencies of airdrops and started to engage in Sybil attacks, aiming to acquire airdrops multiple times through the use of several addresses.
The strategy for airdrops is determined at the discretion of the development team, and the system cannot directly take measures against this trend. This tendency is due to the fact that there is no way to determine whether a single user is operating more than one address.
In response, as a product, measures are being taken to deduce the relationships between addresses and identify and eliminate Sybil attacks, but these measures are still insufficient.
Past Analysis
In a report published on Mirror in March 2023 by Mr. X-explore/WuBlockchain, the Arbitrum airdrop of March 2023 was analyzed. The findings suggest that out of 279,328 addresses, 148,595 were Sybil addresses that received the airdrop. The report highlights that the group that received airdrops in more than 100 addresses was the second largest in terms of profits gained, acquiring a total of 95.72 million ARB.
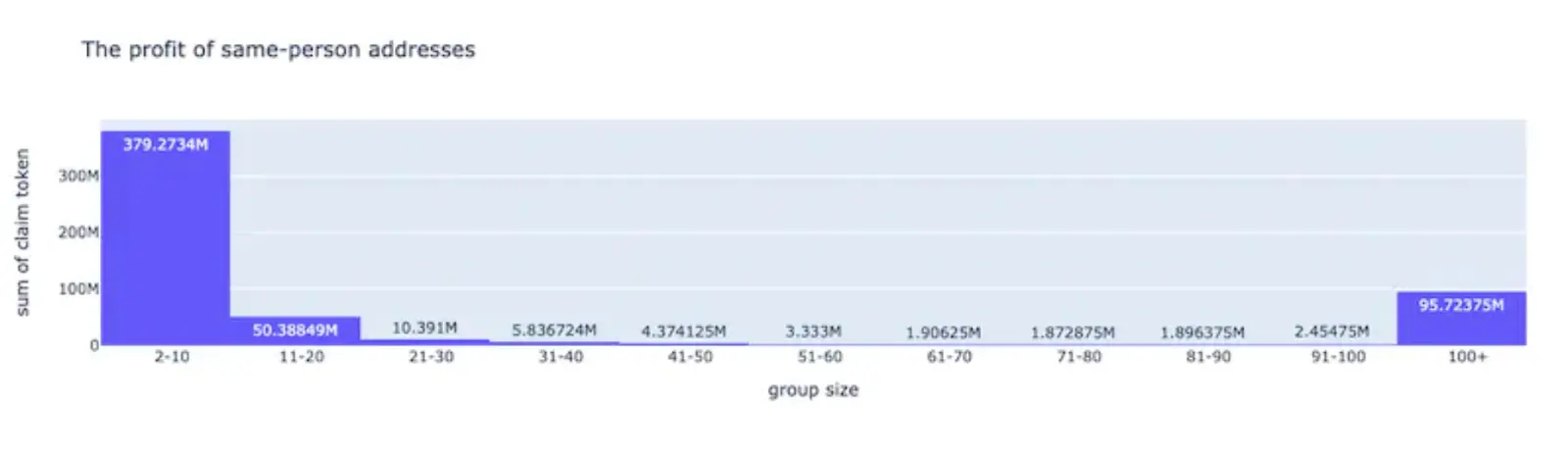
Source:Mirror
The report points out that these addresses effectively evade Sybil detection by dispersing funds across multiple addresses through centralized exchanges (CEX), bridges, and contracts. Although this is not a Sybil attack on the system itself, and therefore does not directly impact the product, the presence of Sybils in the initial distribution of tokens is having a significant impact on the economic ecosystem surrounding the token.
B. Sybil attacks in governance
Token Quantity-Centric Governance and Sybil Resistance
In major protocol DAOs, a political system where voting is conducted based on the quantity of tokens, determining product changes and updates, is common. In a recent Uniswap DAO proposal, the quorum required was 40 million UNI, but the decision could be made with the votes of just the top seven voters among a total of 1,635 voters.
In governance where token quantity is used as the weight of votes, Sybil resistance is adequate because it's challenging for Sybils with false identities to acquire tokens easily. However, this system, based solely on the quantity of tokens, does not reflect the opinions of the majority and has an aspect of plutocracy, differing from a democratic and egalitarian governance system. In May this year, Aragon faced an attack by a highly organized group specializing in extracting financial value through the dissolution of its treasury, representing a different vector of attack from Sybil.
Is One-Person-One-Vote Governance Feasible?
As for the feasibility of one-person-one-vote governance, it hasn't been adopted due to the nature of cryptocurrencies being based on anonymity, allowing one person to use multiple false identities for voting. Since there's no way to know if an individual controls multiple addresses, token quantity-based and progressively decentralized governance seems optimal for protocol DAOs.
In terms of voting systems, methods are being explored to achieve more democratic forms. The bicameral voting system (Optimism) and Quadratic Voting (Gitcoin) are already being utilized as more democratic systems, and Proof of Participation (PoP) could be integrated into systems emphasizing fairness in voting. However, to widely spread democratic voting systems as an infrastructure, other requirements such as resistance to vote-buying must also be met.
C. Sybil attacks in Play-to-Earn (P2E)
Crypto Games and Sybil Attacks
In crypto games, which typically have an in-game economy centered around tokens, rewards are set based on players' gameplay and achievements. A Sybil attack in this context refers to a player using multiple accounts to illegitimately gain rewards or distort the distribution of in-game resources. The risk of Sybil attacks increases when the cost (in terms of time and resources) of the attack is less than the rewards obtained from it.
In Axie Infinity, players need to purchase three Axies to play the game. However, the community found ways to earn significant rewards at low economic and time costs, such as using the 'scholarship' system and multiple devices.
While the mechanism for obtaining rewards in the form of SLP tokens did not directly have a significant impact on the token's price, considering that tokens are part of the motivation for P2E (play-to-earn) gameplay, effectively preventing Sybil attacks can reduce the risk of the game becoming short-lived.
Off-Chain and On-Chain Games
Regarding off-chain and on-chain games, games like Axie Infinity and STEPN, which are popular in the P2E space, operate mostly off-chain. A key issue here is the management of user IDs (wallets).
Even if a game's logic is off-chain, integrating Proof of Participation (PoP) for account authentication can maintain game quality while giving users sovereignty and verifying their humanity. With the proliferation of Account Abstraction (AA), adopting Web3ID logins can efficiently reduce the negative impacts of Sybil attacks (e.g., abuse of multiple accounts) on the game.
In the context of fully on-chain games, integrating Sybil-resistant IDs can incorporate traditional mechanisms like login bonuses and open up new use cases.
Sybil-resistant IDs and their use cases
Sybil-resistant IDs have the characteristic of preventing fraudulent or malicious users from creating numerous fake accounts. Potential use cases that can be realized using this feature are being explored. Although there are already projects adopting it, the spread of Proof of Participation (PoP) itself is not very fast, and its use remains limited. However, with the widespread adoption of PoP, there is hope that the economic sphere as a whole can become fairer.
-
One-Person-One-Vote Voting System
By utilizing Sybil-resistant IDs, it's possible to create a system where each participant has only one ID and can vote only once. This system effectively prevents vote manipulation through fake accounts and allows the reflection of a wider range of participants' opinions, as opposed to a token quantity-based system.
-
Universal Basic Income (UBI) Distribution

Sybil-resistant IDs can effectively prevent the same individual from receiving multiple distributions, allowing issuers to fairly distribute basic income. While there is debate over whether the value distributed through basic income is significant, the distribution scheme itself is feasible with the proliferation of Sybil-resistant IDs.
Sybil-resistant IDs and their use cases
C. Proof of Humanity in User Logins

By integrating PoP authentication within the current Wallet Connect context, applications can effectively prevent the emergence of fake or multiple accounts. This is particularly relevant in the gaming domain, where applications are significantly affected by Sybil attacks, as it can help mitigate negative impacts on the economic ecosystem.
D. Token Distribution
Similar to UBI, in the case of initial token distributions or airdrops, it becomes possible to adjust the distribution quantity per user more fairly. This can also be applied to mechanisms like whitelists during NFT mints, potentially leading to the development of stronger and more cohesive communities.
[Reference] The voting system of Optimism/Gitcoin
Optimism's Layer 2 System
In Layer 2 of Optimism, a concept called the "Optimism Collective" has been introduced as a method to fund public goods in a Non-Plutocratic (non-money-driven) manner. Within this Optimism Collective, there are two different entities, the "Token House" and the "Citizens House," each holding different decision-making powers in their respective DAOs.
In the Token House, votes on protocol upgrades and other matters are based on the number of tokens held. In the Citizens House, a council-style, one-person-one-vote principle is used for voting on retrospective funding for public goods that support the Optimism and Ethereum ecosystems.
The goal of the Optimism Collective is to balance the short-term incentives of token holders with the long-term incentives of public goods development through this bicameral approach (as explained in the original text).
Gitcoin's Quadratic Voting Mechanism
Gitcoin, which aims for sustained funding for products, has adopted a voting system called Quadratic Voting to reflect the opinions of minorities. In this system, the credits needed for voting are squared of the number of votes.
For example, casting one vote costs "12=1 credit," two votes cost "22=4 credits," and ten votes cost "10**2=100 credits." Thus, the cost of casting multiple votes for a single option increases exponentially. After voting ends, funds are distributed from the matching pool for funding according to the final number of votes (not equal to credits).
This design minimizes the influence of large-scale voters, leading to more democratic outcomes. Additionally, Gitcoin integrates the PoP (Passport) to address Sybil attacks where numerous small-value addresses are created, adding further security to the system (as explained in the original text).
Primitives of Proof of Personhood
Positioning of PoP
PoP (Proof of Personhood) ensures that there is only one address that a person can control in a public blockchain. It's possible to plausibly analyze whether an address is controlled by a human by referring to on-chain activities. However, mechanisms that can strictly guarantee this are limited. In this report, we define this as the primitive of PoP.
Primitives of PoP
The primitives of PoP using public chains are mainly known in the following three types:
Iris Recognition
This PoP, introduced by Worldcoin, creates a hash from the iris using specialized hardware and links it to an address. It guarantees one address per person based on the uniqueness of each individual's iris. While this backing is strong, the use of hardware implies geographical constraints and requires trust in the manufacturer.
Social Graph
This PoP uses a social graph indicating relationships between users on social networks and their activities. By creating a graph from the relationships and interactions among users, it considers the social graph-associated addresses as human. While it's challenging for AI or bots to imitate such graphs, binary determination becomes difficult.
CAPTCHA Authentication
This type of PoP distinguishes the uniqueness of participants through their responses to human-specific verification problems. In a well-known example, Idena, participants simultaneously perform a verification called a flip test at a set time. Here, participants are presented with two sets of four-picture combinations and must choose the one with a higher narrative quality. This mechanism effectively prevents duplicate participation in verification while proving one's humanity even in anonymity.
Worldcoin

|
Name |
Worldcoin |
|
Launch |
23/07 |
|
Network |
Optimism |
|
|
|
|
Web |
Overview of Worldcoin
Worldcoin is a project initiated by Sam Altman, the current CEO of OpenAI (@sama). The protocol aims to be the most extensive public network for identity and finance, accessible to everyone regardless of birthplace, background, or economic status. It emerged from the idea that, in the AI era, a means to distinguish between humans and AI in the digital space is necessary.
In Worldcoin, a spherical hardware device called the Orb is used to scan irises, thereby creating proof of humanity. This process assigns a unique identifier to each individual, known as WorldID. The issuance and verification of WorldID are conducted using zero-knowledge proofs, ensuring that users' personal information is not exposed and their privacy is protected. This biometric authentication acts as a PoP (Proof of Personhood) and is highly authentic. As a result, people holding an ID periodically receive WLD coins as a form of Universal Basic Income (UBI).
The main applications of the Worldcoin project are as follows:
World ID - A digital ID with PoP functionality. It maintains privacy and allows self-custodial management, enabling users to log into websites and DApps.
World App - An application that enables the acquisition of IDs, PoP authentication, and asset management.
Worldcoin (WLD) - A coin that owners of WorldID can receive. It aims to prevent duplication of receipt and provide equal economic opportunities by basing it on PoP.
World ID Overview
World ID
The issuance of World ID is conducted through a spherical device called the Orb. The Orb is manufactured by a software/hardware development and manufacturing company based in San Francisco, USA, named "Tools For Humanity (@thf_technology)."
By using the Orb, users can authenticate themselves through an iris scan, and as a result, obtain a World ID linked to a specific address that proves their humanity. The flow for registering a World ID is as follows:
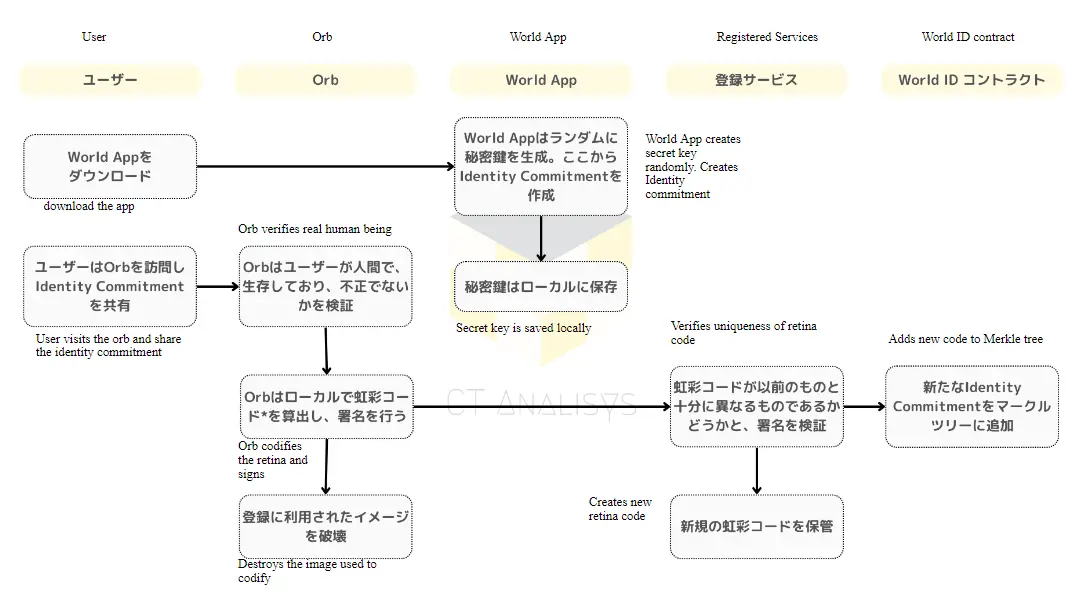
Interpreted & made by author(original:Worldcoin Docs)
To use World ID, users must download a dedicated application called "World App" and generate a private key and an Identity Commitment (similar to a public key) within the app. Next, they perform an iris scan using the Orb, and the resulting hash (iris code) and Identity Commitment are verified by a registration service (sequencer node).
It checks whether the iris code used is not a duplicate of an existing registration. Once the verification is successfully completed, users can obtain a World ID, which can be used in multiple applications. In applications compatible with World ID, users generate a Zero-Knowledge Proof (ZKP), through which they can prove their Proof of Personhood (PoP).
Worldcoin User Statistics
Number of Worldcoin wallets
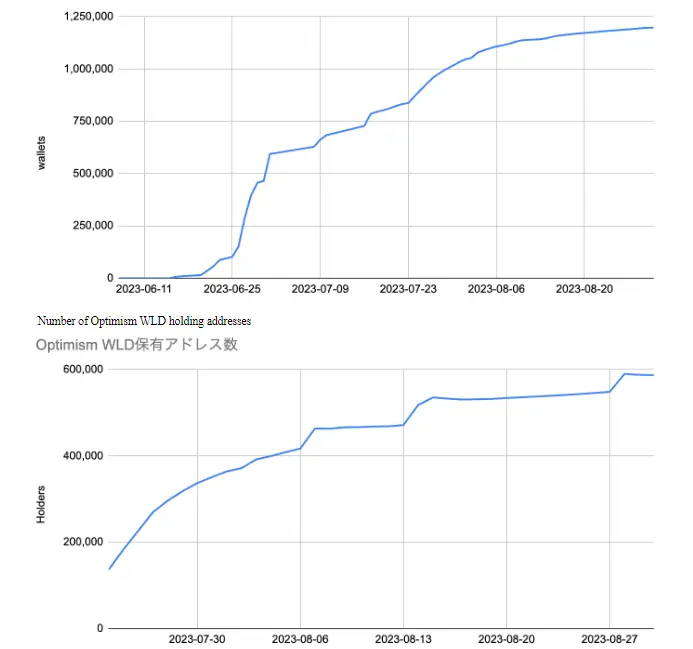
Data: dune
As of the end of August, the total number of Worldcoin wallets was 1.2 million (according to Dune Analytics), while the number displayed in the app was 2.26 million, indicating a rapid increase in the number of users over a few months since launch. The WLD coins, which can be obtained by completing iris scan authentication, have nearly 600,000 holders according to the holder-based figures, signifying significant growth in both the number of holders and the pace of increase. With the introduction of applications utilizing World ID in the future, there is an expectation for the emergence of use cases beyond just acquiring the ID.
BrightID
|
Name |
BrightID |
|
Launched |
19/02 |
|
Network |
IDChain |
|
|
Overview of Bright ID
Bright ID is a network of IDs centered around social IDs, designed to prove humanity to applications. It utilizes a graph-type database to create and analyze social graphs. By proving the uniqueness of users through peer relationships, Bright ID provides Sybil resistance to IDs.
Users set up their ID using a name (pseudonyms allowed) and a photo, and by building connections with other ID holders, they can autonomously prove their identity.
When establishing new connections, users select from three options regarding their relationship with the other party: 'know well,' 'just met,' or 'suspicious person.' The validity of the relationship is confirmed by the matching of responses from both parties. If the responses conflict, it indicates that one party has chosen an incorrect option, negatively impacting the verification of the ID's authenticity.
A verified BrightID is compatible with linking to currently 18 applications, including fundraising apps like Gitcoin and clr.fund, and voting apps like Snapshot and 1Hive. By completing the linkage with these applications, users can easily prove their uniqueness as human beings to these platforms.
Proof of Humanity
|
Name |
Proof of Humanity |
|
Launched |
21/03 |
|
Network |
Ethereum |
|
|
|
|
Web |
Overview of Proof of Humanity
Proof of Humanity (PoH) is a social-based ID verification system (registry) that combines a public key and its owner's trust model (Webs of Trust) based on user-to-user trust, reverse Turing models, and conflict resolution. It is designed by Kleros as a tool to achieve Sybil resistance. The goal of PoH, similar to other Proof of Personhood (PoP) IDs, is to be integrated into new use cases that require Sybil resistance.
To acquire PoH, users must register the following in the registry: A. Display name (required), B. Full name (optional), C. Facial photo (required), D. Video holding a paper showing the address (required), and E. Deposit a certain amount of money. The registered profile needs to receive Vouching (endorsement) from other users, and upon passing this, it can be used as an official ID.
One of the established use cases is Universal Basic Income (UBI). Addresses that have completed PoH verification receive UBI tokens, which accumulate every second. This system is expected to be used for integrating a borderless, democratic, autonomous, decentralized organization and financial system. UBI is not backed by any collateral but is based on a fair distribution mechanism of one address per person and accumulates over time, representing temporal value. Purchasing UBI is presented as synonymous with buying the temporal value of another human being.
Comparison of Identity Products
|
Worldcoin |
BrightID |
Proof of Humanity |
|
|
Overview |
PoP Financial Network |
Social ID Network |
Trust-based ID verification system |
|
Development |
Worldcoin Foundation |
BrightID Contributors |
Kleros |
|
Verification Methods |
Iris Recognition |
Social Graph |
Trusted Video Verification |
|
Verification Flow |
Iris scan using Orb |
Establishing Connections |
Video registration & user insured |
|
Centralized Risks |
Orb Manufacturers |
Social Graph algorithms |
Low - peer based |
|
Geographic constraints |
Yes (needs the orb) |
None |
None |
Worldcoin requires specialized hardware for iris scanning and generating iris hashes. This necessitates a higher degree of trust in the hardware's design compared to systems like BrightID or Proof of Humanity, and also raises concerns about the centralization of the system. Moreover, geographical limitations may prevent some people from accessing Orb locations to create their ID.
Currently, Tools For Humanity is the primary manufacturer of this hardware, and while there are plans to decentralize production in the future, there are concerns that TFH may remain the central actor in manufacturing. Additionally, there are fears about the issuance of World IDs through unauthorized hardware.
On the other hand, BrightID uses a social graph-based authentication system that requires known connections of the user. This method is said to potentially offer more benefits to users with many connections than biometric authentication.
SSO (Single Sign-On) applications that aggregate user information
SSO & ID
What is SSO?
SSO (Single Sign-On) is a mechanism that allows users to access multiple web services using a single set of credentials, like a Google or Twitter account, without needing separate IDs and passwords for each service. This technology has become widespread even outside the context of public blockchains.
However, many of these SSO solutions are centrally managed by large tech companies, which, while convenient, base user privacy and data security on trust in these corporations.
In Web3 web applications, users can connect their wallets and use their addresses as identifiers to access services across different platforms, enhancing privacy and security. However, this can limit the functionality and business development of the applications since they cannot distinguish users' identities.
Aggregation of On-Chain (Off-Chain) Identities
While PoP (Proof of Personhood) focuses on the fundamental aspect of identity verification, aggregators are being developed to add SSO-like functionality using selectively disclosable credentials and qualifications associated with an address.
Currently, user screening by applications is limited when only addresses are used, relying mostly on public information related to the address (like ERC20 balances or ERC721 holdings). This limitation restricts user optimization and service expansion for applications.
Gitcoin Passport aggregates various IDs and performs human scoring, creating opportunities for civil resistance and other credential verifications for integrated products. Quadrata Passport enables the verification of KYC and AML for addresses, which is gaining attention for its potential to facilitate business operations under regulation and attract traditional financial players.
Gitcoin Passport
|
Name |
Gitcoin Passport |
|
Launched |
22/08 |
|
Network |
Ceramic Network |
|
|
|
|
Web |
Gitcoin Passport is a product that aggregates PoP (Proof of Personhood) IDs and Web 2.0 IDs. By issuing a passport, users can prove their humanity and online reputation to third parties while maintaining their privacy. Gitcoin Passport is a tool for issuing and managing verifiable credentials (VCs) and also serves as an interface for sharing these credentials with other applications and organizations.
Users can create their own passport through the Gitcoin Passport App. By authenticating their online identity with products integrated with Gitcoin Passport, they can earn stamps (VCs). These stamps include proof of ownership of ENS or Lens, Twitter, GitHub, Discord accounts, and can also be used for proving online reputation and humanity, with integrations like BrightID and Proof of Humanity.
Using the Gitcoin Passport App, users can create a Passport (DID) and link VCs to it, and also earn a humanity score from Gitcoin. For operators of products, integrating Gitcoin Passport allows them to screen for addresses with high Sybil resistance and easily verify whether a user is a real person. Furthermore, it enables the creation of more specific access gates based on POAP holdings or scores, not just verification of humanity.
VC issuance and verification flow of Gitcoin Passport
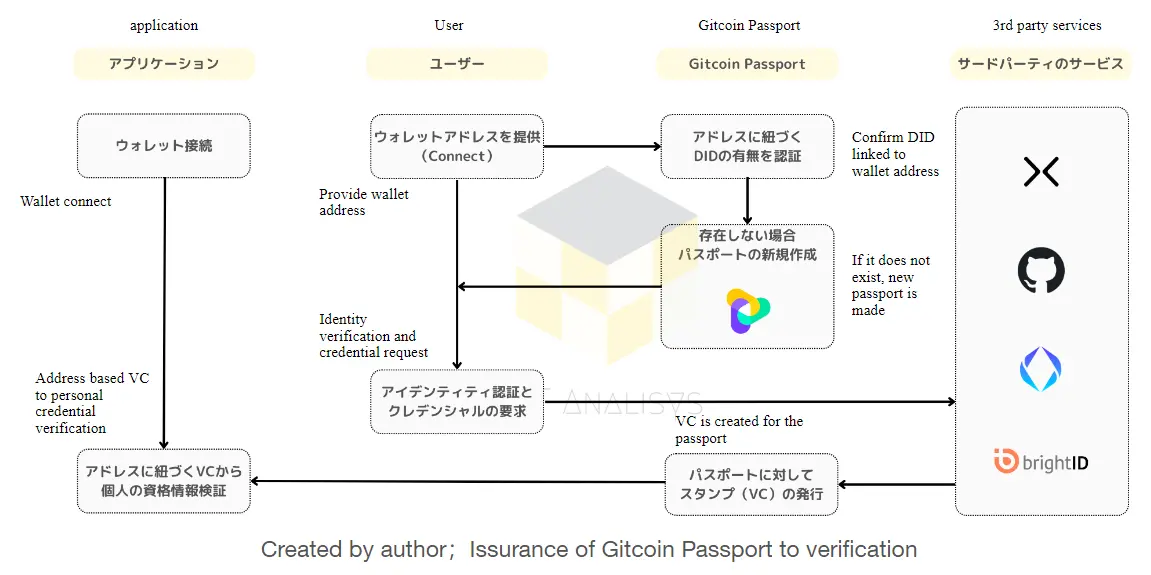
The flow for users to issue a Gitcoin Passport and verify credentials is generally as described in the above figure:
Verification of Passport Ownership:
When a user connects their wallet to the Gitcoin Passport website, Gitcoin Passport checks if a passport (DID method) associated with this address exists. If not, a passport linked to the user's address is created at this stage. Data is stored on the Ceramic Network.
Authentication of Various Credentials to the Passport:
When a user completes authentication with compatible online identity services like CyberConnect, GitHub, ENS, BrightID, etc., Gitcoin signs this and issues a VC (Verifiable Credential) as a stamp (Ceramic). This is in the form of a signature for authentication, and Gitcoin does not retain user data.
Integration by Applications:
Applications integrating Gitcoin Passport can verify the personhood of an address by collectively verifying its multiple credentials. Screening and weighting of addresses based on specific VC holdings are envisioned as typical use cases.
Quadrata Passport
|
Name |
Quadrata |
|
Launched |
22/07 |
|
Network |
Arbitrum & 6 other networks |
|
|
|
|
Web |
Quadrata Overview
Quadrata is a system that allows minting of SBTs (Soulbound Tokens) related to ID information for specific addresses. This passport system enables the association of government-issued IDs while protecting privacy. It uses "Persona" for authentication, allowing users to prove KYC/AML information to third parties without revealing actual information.
A significant downside of Quadrata is that it requires the submission of a government-issued ID, making it inaccessible to people who do not possess such an ID. However, it offers the advantage of providing higher confidentiality and a trustless environment in use cases where KYC is demanded, such as the issuance of legal RWAs (Real-World Assets).
|
Factor Types |
Explanation |
|
DID |
Civil Resistance ID - Proof that a wallet address is associated with only a single entity |
|
AML |
Quantifying the AML risk of passport holders with a score from 1 to 10 |
|
COUNTRY |
Defining the country of issuance for government IDs using the 2-letter country codes as defined in ISO 3166, such as 'US', 'RU', etc. |
|
IS_BUSINESS |
Defining whether the passport holder is an individual consumer or a business entity |
|
ACCREDIT_INVESTOR_US |
Determining whether someone qualifies as an accredited investor in the USA |
|
CRED_PROTOCOL_SCORE |
Scoring the likelihood of a loan borrower being liquidated in the next 90 days with a score ranging from 300 to 1000, using the Cred Protocol credit score |
[Supplement] Information disclosure through DID (Decentralized Identity) and ZKP (Zero-Knowledge Proof)
The report explains that Gitcoin Passport and Quadrata Passport, as issuers of DIDs (Decentralized Identifiers), enable users to autonomously store a list of identity information within their addresses. Users can sign and disclose any of the credentials stored in the DIDs associated with their address, allowing third parties to verify them.
Although slightly deviating from the main theme of the report, the report also introduces the concept of identity solutions using zero-knowledge proofs (ZKPs), which may offer greater flexibility than current ID aggregators.
Zero-Knowledge Proof-based IDs and Use Cases
An alternative that is gaining attention as a more superior solution involves creating zero-knowledge proofs for any assertions, instead of disclosing and verifying information. This method is particularly valuable in the field of self-sovereign IDs, where it's challenging to simultaneously achieve personal qualification proof and personal information protection. By using ZKPs, the privacy of the holder can be fully protected.
Products in this area include Polygon ID, Sismo, Holonym, and zkSBT (Manta Network), among others.
The basic idea is that a user creates a zero-knowledge proof (ZKP) for a certain claim, and the verifier of this ZKP can then verify whether the claim is true. For example, to prove that one is over 20 years old, typically, a government-issued ID is required. However, instead of presenting the ID, presenting a ZKP created with the claim and the user's signature can prove this without revealing any information about the ID (thus maintaining complete anonymity).
Combining zero-knowledge proofs with IDs can potentially create stronger use cases. In activities like voting or petition signing, this method enables the disclosure of information based on unique personhood without revealing any personal identity details.
Considerations and Summary
Summary & Considerations
In this report, we have explained the primitives of Proof of Personhood (PoP) that enable the creation of Sybil-resistant IDs, and products that offer Single Sign-On (SSO) passports, which aggregate user information and store various credentials. Sybil resistance is a highly important feature in public blockchains, an anonymous and decentralized network. PoP, which proves the personhood of an address, could greatly influence identity management in the digital space and the construction of social systems.
We have organized the points of expected new use cases centered around Sybil-resistant IDs as follows:
Strong guarantee of address personhood (PoP)
More extensive experiments with Universal Basic Income, backed by fair and transparent distribution mechanisms (individual x elapsed time) such as WLD.
More accurate advertisement delivery systems ensuring one view per person, effectively preventing duplicate reward payments.
More democratic voting systems with one person, one vote.
Construction of fairer resource distribution systems in token sales and in-game economies.
Protection of user privacy using Zero-Knowledge Proofs (ZKP)
Anonymity in voting and signature campaigns. Even for expressing sensitive opinions, there's no need to risk revealing one's identity.
Issuance of digital IDs purely using public blockchain infrastructure, leading to high portability and interoperability across applications.
Anonymization of airdrops.
Anonymization of KYC processes, allowing access to regulated services without revealing one's identity.
These are just a few examples, but with the large-scale implementation of PoP, the range of user self-sovereignty could expand from just owning assets to also encompassing the realm of IDs. Furthermore, with the proliferation of ZKP, more self-sovereign and flexible disclosure of information could be realized.
Sources
Worldcoin Whitepaper - https://whitepaper.worldcoin.org/
Advanced Analysis For Arbitrum Airdrop — X-explore - https://mirror.xyz/x-explore.eth/AFroG11e24I6S1oDvTitNdQSDh8lN5bz9VZAink8lZ4
Aragon Association Takes Action to Safeguard the Mission of the Aragon Project and its Community of Builders - https://blog.aragon.org/aragon-repurposes-dao-to-ensure-treasury-serves-its-mission/
BrightID - BrightID - https://brightid.gitbook.io/brightid/
Gitcoin Grants – Quadratic Funding for the World | Gitcoin Blog - https://www.gitcoin.co/blog/gitcoin-grants-quadratic-funding-for-the-world
What is the Optimism Collective? | Optimism Docs - https://community.optimism.io/docs/governance/
Introduction to Quadrata - Quadrata Integration - https://docs.quadrata.com/integration/introduction/introduction-to-quadrata
proof-of-humanity-registry-policy.pdf - https://blog.kleros.io/content/files/ipfs/Qmc7ag5XohnSAozvsKsLCUbvaFyasyLtyi3H7g3mmxznPU/proof-of-humanity-registry-policy.pdf
Introducing UBI: Universal Basic Income for Humans - https://blog.kleros.io/introducing-ubi-universal-basic-income-for-humans/
Gitcoin Passport: Identity Verification Built on Ceramic - https://blog.ceramic.network/gitcoin-builds-passport-on-ceramic/
What do I think about biometric proof of personhood? - https://vitalik.ca/general/2023/07/24/biometric.html
Disclaimer
This report is not intended, in any way, to constitute an offer to buy securities (including virtual currencies and tokens analogous to them). Additionally, this report is purely a part of an information provision service and should not be regarded as financial or other professional advice. The information provided in this report should not be relied upon. This report should not be interpreted as advice or a recommendation concerning securities (including virtual currencies and tokens analogous to them). The providers of this report do not take into account the suitability for individual investors (investment objectives, financial circumstances, or specific needs). Therefore, when investing based on this report, it is recommended that each investor seek independent financial, legal, and tax advice before making an investment. Investors should be fully aware that these financial products (including virtual currencies and tokens analogous to them) may be subject to price fluctuations. Furthermore, the quantitative data contained in this report does not guarantee or promise the principal or a certain return on these financial products. Please be aware that depending on the situation, there is a possibility of losing part of the investment amount.
All copyrights of this report belong to our company or those who provided the information to our company (hereinafter referred to as 'Information Providers'). Without the prior written consent of our company or the Information Providers, it is not permitted to reproduce, retransmit, distribute, sell, distribute, publish, broadcast, circulate, commercially use, modify, or alter this information. In addition, the user agrees not to use this report for illegal purposes. Users who have downloaded this report agree not to delete or remove the copyright or other notations of the report.